
Today, the DST Root CA X3 certificate expired, leaving many devices on the internet having issues connecting to services and certificates that use this Root CA, including those using Let’s Encrypt certificates.
Some of these problematic devices include Samsung Galaxy phones, iPhones, VDI zero and thin clients, and even Sophos UTM firewalls.
In my environment, I noticed a number of issues when browsing to websites that use the free Let’s Encrypt certificates, as the Web Protection Web Filtering service on my Sophos UTM firewall would report the certificate has expired and not allow me access to the websites using it.
The Problem
Let’s Encrypt originally used the “DST Root CA X3” certificate to issue Let’s Encrypt certificates. However, as time has passed and the service has been used more, they now use “ISRG Root X1” and “ISRG Root X2” as Root CA’s and “Let’s Encrypt R3” as an intermediate certificate.
Older devices may be using the older Root CA which expired today (September 30th, 2021). Please see https://letsencrypt.org/docs/dst-root-ca-x3-expiration-september-2021/ for more information.
The Fix
To fix this issue, you need to add the 2 new Root CAs to your computer or device.
Root CA Certificates (PEM format):
Intermediate Certificate (PEM format):
You can download them by clicking the links above or go to https://letsencrypt.org/certificates/ for more information and to download if you don’t trust the above links.
After downloading and adding these Root CAs and the Intermediate CA to your computer or device, you should have the full certificate chain to validate the Let’s Encrypt certificates. You only need to add the two root certificates. The Let’s Encrypt certificates that are used on websites that you visit and that you might have deployed on your servers should now work without any issues.
If you’re still having issues, you can try deleting the “DST Root CA X3” certificate from your existing Root CAs. Also, you may need to close and reopen any software and/or browsers for it to work with the new certificate.
HTTPS Scanning/Filtering Firewall Fix (Sophos UTM as example)
If you have a firewall that scans HTTPs traffic, you’ll need to add the two root certificates above to the HTTPS Certification authority list.
As an example, to fix this on the Sophos UTM firewall, follow the instructions below:
- Download the 3 certificates above.
- Log on to your Sophos UTM
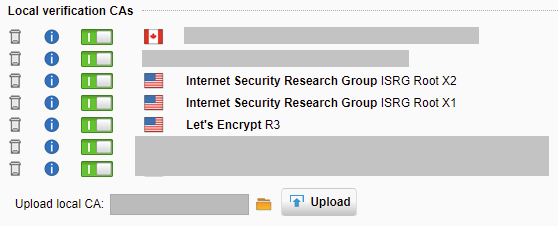
- Navigate to “Web Protection”, “Filtering Options”, and “HTTPS CAs” tab.
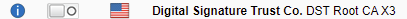
- Disable the old “Digital Signature Trust Co. DST Root CA X3” Certificate in the list.
- Using the “Upload local CA”, browse to and select 1 of the 3 certificates, then click upload.
- Repeat step 5 for each of the 3 certificates listed above.
- The issue has been fixed! You should now see all 3 certificates in the “Local verification CAs” list.
The steps should be similar for other firewalls that provide HTTPS Scanning and Filtering.
[…] PLEASE NOTE: If you are experiencing this on September 2021 or later, please see DST Root CA X3 Certificate Expiration Problems and Fix. […]
Thanks Stephen. Your article last year fixed my Comodo cert expiring issue and now you have fixed my Let’s Encrypt issue. In my case I needed to restart the UTM for the certs to come into effect. Thanks so much
Thanks for the precise and to-the-point information. This was bugging my email client since yesterday and besides all the discussions of concerned admins, no one except you seemed to bother providing a link to the three relevant certificates. A one minute fix.
Hi Stephen,
I ran into this problem and thankfully I found your post. CAn you go into detail about how to fix this problem? I downloaded the files but I have no idea what to do with them.
thank you every much. no where it is mentioned as perfectly as you did
genio! gacias por la solucion!
You’re welcome! Glad it helped!
You saved my day…
This works perfectly… not sure until when but it works
Thank you Stephen! I’ve had two support requests caused by this issue in the last 24 hours. Your explanation and fix description is detailed and thorough. Thanks again.
Thank you so much: you saved may day !
In 5 minutes everything was again working fine with my HTTPS filtering/scanning on my Sophos UTM 9 appliance.
Very nice to see there are still people sharing valuable information…
This worked great! The “connection not secure” error message for visiting certain sites went away. I use a Mac, and after downloading the 3 certificates I had to follow the quick instructions at the link below and that did the trick:
https://support.apple.com/guide/keychain-access/change-the-trust-settings-of-a-certificate-kyca11871/mac
Thanks again, Stephen
Thank you Stephen! Phenomenal fix. I am a beginner end user and have Windows 7 (groan). However I determined in applying Stephen’s fix the DER files worked. The PEM files would not. So for those of you that are attempting to apply the fix don’t despair. After restarting my computer with the DER files so far I have had no issues. I also live in the USA.
Hope this information will help and encourage others to give it a try.
So grateful I found you and the fix!
I run mantry.com, Stephen gave me 1 minute of guidance over chat along with the thorough instructions on this blog and I was able to fix the DST Root CA X3 Certificate Expiration Problem. He made my week!
Hello Stephen
I just downloaded the files, but I don’t know what’s next
Do I need to reemplace the tree files on specific folder on my computer?
Greetings from Mexico
Hi Omar,
The Root CAs and Intermediate CA need to be added to your devices Certificate store. As an example, if this was windows, you’d add the Root CAs to the System’s “Trusted Root Certification Authorities” store, and the Intermediate to the “Intermediate Authorities” store.
Cheers,
Stephen
According to Sophos, as of 10/1/21 at 19:00GMT an update was released and a restart is required because certain services such as web proxy cache the previously loaded certificates.
From https://support.sophos.com/support/s/article/KB-000042993?language=en_US
“The CA Data bundle for UTM has been released. All Sophos UTMs should have received & are updated.
This bundle removes the expired Let’s Encrypt X3 CA from both the UTM cert store (used by web proxy, email) and WAF. This should automatically resolve the issue for both WAF & Email.
For awarren [sic] http (web proxy) it may require a restart before the issue is resolved. That’s because the proxy caches the CAs and requires a restart to reload.
Sophos Firewall web proxy – Hotfix roll out started to address issue Friday, Oct 1, 2021 19:00 GMT”
Hey Brent! Thanks for the update!
Thank you Stephen! These steps helped me resolve my issues I’ve been trying to resolve these past two days
BLESS THIS MAN, HE’s DOING THE GOOD WORK!
i m on a mac and it showed cert not trusted. saw
Paul Arbaje comment at #12. did this fix and it worked. tks stephen and paul
how to delete old DST Root CA X3 Certificate in my windows 7 OS ?
Hi. Thanks for this !. this drove me nuts for a day until i found this blog. All fixed now and back to normal ! Thanks Stephen.
Could figure out why I couldn’t access so many websites yesterday. Thanks so so much for this post. You’re a life saver. Your advice worked like a charm.
Thanks Stephen!
Greetings from Spain
What a snafu this Let’s Encrypt root certificate has been for me, that completely took me by surprise! I have attempted to manually update the certificates, as instructed here in Stephens article as wel as from the commenters, using KeyChain Access etc, but with no success.
I am running an old setup with Mac OS X 10.6.8, using Firefox 48. My knowledge of using the OS is above average in the sense I am not hesitant to use Terminal and Keychain Access. If someone would be kind enough to post some straightforward instructions I would appreciate it. Otherwise, I am wondering what all of this means for my ability to access the internet moving forward?
Please,
I have a problem with CentOS 6 and the OpenSSL version is 1.0.1 and it needs 1.1.0 or higher according to the Letsencrypt website. I use a network proxy server with navigation controls in SQUID. We are not able to navigate.
Is there any solution for CentOS 6 or only on CentOS 7?
Thanks
Do you just copy the three files into the “certifi” folder within SABnzbd? I tried that and DLs still don’t start.
Worked! Thank you for providing the new certificates, so grateful. I’m on Mac OS 10.11.6 and started worrying that my computer was about to become useless.
Steps I used to install:
– clicked on the files above to download
– opened the Downloads folder, found the downloaded files
– double clicked each of the 3 .pem files to add them to Keychain Access. (Ignore the extra files that were downloaded)
– in KeyChain, double click the two new ISRG certificate, expand the Trust dropdown, set “When using this certificate” to Always Trust.
Hi, I’m trying to fix this problem on my uncle’s old computer, and I can’t even get the Lets Encrypt page to load. It’s an old Dell Dimension 4500 running XP (I can hear the laughter now!). Are there any work arounds you can suggest or is it simply too old to fix? Thanks!
Nice one 😉 thanks Stephen
WoW !! I’m on mac 10.9.5, and half my regular sites just got bungled – thankfully this was a super easy fix !! Just opened “Keychain Access.app” , selected “System Roots”, and dropped in the 3 “.pem” files ! Presto Chango ! Thanks clever stranger !!
Fixing the DST Root CA X3 Certificate expiration issue on Mac step by step:
1. Download the 3 Certificates onto your Mac like the article states above.
2. Open Applications > Utilities > Keychain Access.
3. Unlock Keychain Access if locked, by clicking the lock icon and entering your password.
4. Drag the 3 Certificates into Keychain “login”
5. Double-click a certificate, it will open a smaller window with “Trust” and “Details”. (pop-up menu)
6. Click on the “Trust” arrow to expand it.
7. Click to expand the pop-up menu near “When using this certificate”.
8. Choose the option “Always Trust” from the pop-up menu.
9. Drag the Certificate again, from “login” into “System”
10. Do this with all 3 Certificates.
Hope this helps! Thanks for the article Stephen, awesome website. Thanks for the links and info from everyone who commented that helped with writing these steps. Best of luck to all!
Hi Stephen
I ran into this problem and thankfully I found your post. I downloaded the files and import it’s to my computer certificate root via mmc tools and solved my problem completely .
very thanks Stephen
Thanks for easy fix manual. Everything works again. 🙂
Great job hope you get hired lol. I’m running my old XP for my ham radio work and you are the only one on the internet who seem to have a clue! Google does not respond or my security people in India “Norton 360”
Tried to visite the cert site, however, Google indicates they are not safe! Great job!
thanks man, think this will resolve Thunderbird mailing problem with these certificates, thank you !
The Root CA Certificate links provided are inaccessible because of the very problem I came here to find out how to solve. As of September 30th I can’t access half the internet including Let’s Encrypt website and files.
Problem: I can’t drive my car because the gas tank is empty.
Solution: Drive to the gas station and get more gas.
Thanks for this. However, when I click on the links you provide, I cannot open them due to the
“Your Connection is Not Private” message blocking access. Am I misunderstanding what I am supposed to do?
Depending on your browser, you may need to click on “continue anyways”.
Hi Dwells,
If it’s telling you they aren’t secure, click on “continue anyways” or use a different browser.
I found your blog due to being hit by this issue and searching for answers. You, alone of all the pages I looked at, gave me clear help.
This issue affected me by preventing me from accessing some HTTPS sites. Wikipedia was one. It affected all browsers on my systems – even Firefox, which handles its own internal certificates. This was on both Windows Vista and Windows 7.
Downloading the three certificates you linked to , and then installing them via going to Internet Options (under networks and sharing) in the control panel was the first step in making my affected systems work again. (thank you very, very much!).
The reason I’m writing, other than to say thank-you, is because it was not the only needed step, and in case others have the issue, I want to describe it and the fix. The issue was Firefox (and, I assume, other browsers that do internal certificate management.). The long and the short of it is I was still having the problem in Firefox (two different versions on two different systems under different OS) though not on other browsers. So, I installed the certificates you linked into firefox, restarted it, and bingo, fixed.
Thank you again for your post.
OMG dude it worked!!!! I downloaded exactly what I needed and fumbled around until I got the settings right. Thank you so much for the simple explanation and the useful fix.
Dude, I seriously thought my computer was failing. This is wonderful information and you are pretty much a god right now. JK, but seriously……thanks.
Just one question. I installed only the two certificates- not the intermediate ones- that solved my problem. I am on a Mac. Do I need the intermediate certificate? Thank you again!
Hi Carmen, you only need the root certs. The intermediate is not required.
Worked just fine for me on Sophos UTM 9.707-5. The only thing that has been different to your workaround was that UTM did not show me the old Digital Signature Trust Co. DST Root CA X3. Idk if it just disappeared because it expired…
Thanks!
The application is hosted in the IIS on remote server.So the certs needs to be installed on the remote server right? not on every client machine that uses that site?
The root certificates need to be on each client.
Hello
How can you fix this on a MAC using Catalina
Chrome and Safari wont let me to to your site
Only Firefox
I see you are very helpful
what do I do when I download those files
Hello
I followed the instructions on comment 33 and one of the sites on Chrome I go to worked will test others
I’ve been pulling my hair out on this!!!
Thank you everyone!!!!
@Moritz Müsse: Yes and no. Sophos removed the DST Root CA X3 in the meantime:
https://support.sophos.com/support/s/article/KB-000042993?language=en_US
fantastic! thanks for such a great write up and resolution.
worked a treat on OS X El capitan 10.11.6. (comment 33 spot on)
also with el capitain 10.11.06,
SUPER!Thank you so much!!
#29 worked
Erik Doeff says:
Thank you Erik!!
WINDOWS 10 – DETAILED STEPS
Posting exact steps of what worked for me. Thanks for this post.
1. Download the .DER versions of the 3 certificates listed above. Filenames you should end up with are
isrgrootx1.der
isrg-root-x2.der
lets-encrypt-r3.der
2. Open Windows Settings, search for ‘certificate’, select ‘manage computer certificates’ (requires elevation)
3. Navigate tree view: Certificates – Local Computer > Trusted Root Certification Authorities > Certificates. Sort by “Friendly Name” column. Look for ISRG ROOT X1 and ISRG ROOT X2.
I was missing both.
4. Right-click on Certificates folder in the tree view, and select all tasks > import.
5. It will prompt you for filename. Select “isrgrootx1.der” file downloaded in step 1. Import.
6. Repeat for filename “isrg-root-x2.der”.
Note: after import, it appears that there are duplicate entries for these – I see ISRG Root X1 and ISRG Root X2 each listed twice. I don’t think this is a problem, but I don’t understand it.
7. Find expired certificate “DST Root CA X3” in the table. Right-click > delete.
8. Navigate tree view: Certificates – Local Computer > Intermediate Certification Authorities > Certificates.
9. Right-click Certificates folder, select all tasks > import.
10. At file prompt, select the “lets-encrypt-r3.der” file downloaded in step 1. Import.
11. Reboot system.
QED
FYI I use Vivaldi.
Greg
Just wanted to say thanks! Your post worked like a charm. I appreciate your taking the time to post this for all of us.
Stephen, Erik Doeff (29), KP (33), I love you all, it WORKS !!!
Thanks so much, so glad for helpfullness, espacially to Stephan Wagner, KP for details on macos
How do you install the PEM certificates in Windows 7? I’m using Windows 7 Professional 64-bit. I tried to google it but almost every website refuses to load because of this error.
Thank you so much Stephen. You are a lifesaver!
Never mind, I figured it out. For Windows 7 you need the certificates in DER format. Then just double click them and install them.
It is really helpful. It solved my issue with some https web site. Thanks a lot.
** Big Thanks to Greg’s comment, I used his method almost step by step… with only a few differences as noted below, as I’m using Windows 7 Home Premium SP1. I’m using Greg’s post as a template. Thanks to Stephen also for the original post. **
Windows 7 Home Premium Service Pack 1 (SP1) – DETAILED STEPS :
1. Download the .DER versions of the 3 certificates listed above. Filenames you should end up with are
isrgrootx1.der
isrg-root-x2.der
lets-encrypt-r3.der
NOTE : I used Firefox browser (old version) to download the files. First it wouldn’t let me download the files from letsencrypt.org using Chrome … of course … because of the very problem I was trying to fix … can’t load letsencrypt.org at all in Chrome. Then I used Firefox to go to : https://letsencrypt.org/certificates/ — From there, I tried clicking on the file links. Normal click didn’t work — Firefox kept telling me those certificates are already installed. I had to Right-Click on the proper .DER file links and Choose ‘Save Link As…’ … this way I was able to download all 3 files and save them to my desktop.
2. Open Windows Settings, search for ‘certificate’, select ‘manage computer certificates’ (requires elevation)
NOTE : Not sure what Greg meant by ”Windows Settings” … I tried searching for ‘certificate’ or ‘manage computer certificates’ or ‘certificate store’, nothing. So I simply pressed Windows Key+R and wrote ”certmgr.msc” (without the quotes). This opens Windows Certificate Store directly. (The windows key is the one that has the windows logo on it, on your keyboard. You hold that key and the letter R at the same time)
3. Navigate tree view: Certificates – Local Computer > Trusted Root Certification Authorities > Certificates. Sort by “Friendly Name” column. Look for ISRG ROOT X1 and ISRG ROOT X2.
I was missing both.
NOTE : In my case it was under Certificates – Current User … this serves the same purpose.
4. Right-click on Certificates folder in the tree view, and select all tasks > import.
5. It will prompt you for filename. Select “isrgrootx1.der” file downloaded in step 1. Import.
NOTE : This opens the Certificate Import Wizard. You can browse to your downloaded files. For convenience, I saved the 3 certificates on my Desktop. Important : After clicking ‘Browse…’, it only shows .cer and .crt files by default. At least in my case. You have to select ALL FILES for it to show your DER files. You click where it’s written ‘X.509 certificates’ … (on the bottom, next to File Name:) … you scroll down to select All Files. Another important note : it wanted me to confirm the installation of the root certificates. Warning message saying something like ‘cannot verify bla bla’ … of course I could have been concerned, but since I downloaded the certs directly from letsencrypt.org I didn’t care. I researched Let’s Encrypt before and they seem trustworthy. They provide certs to 260 million websites. So I clicked YES and the certs were successfully installed.
6. Repeat for filename “isrg-root-x2.der”.
Note: after import, it appears that there are duplicate entries for these – I see ISRG Root X1 and ISRG Root X2 each listed twice. I don’t think this is a problem, but I don’t understand it.
NOTE: unlike Greg, I didn’t have any duplicates after installation. Doesn’t matter to me anyway, as long as it works.
7. Find expired certificate “DST Root CA X3” in the table. Right-click > delete.
NOTE : I didn’t delete that expired cert and everything still works (in my case). If anything starts acting funny in the future, it might be a good idea to try deleting it. After all, the certificate is expired and should serve no purpose, I guess (?) Not being very knowledgable, I just take no chance — as long as something works, I don’t take any extra step.
8. Navigate tree view: Certificates – Local Computer > Intermediate Certification Authorities > Certificates.
9. Right-click Certificates folder, select all tasks > import.
10. At file prompt, select the “lets-encrypt-r3.der” file downloaded in step 1. Import.
NOTE : Same steps as above, when we imported the root certs earlier.
11. Reboot system
NOTE : In my case, I didn’t reboot my computer. I didn’t even restart Chrome browser. And everything worked fine instantly ! Was able to access Wikipedia again, plus any other site that was causing problems before. Note that I only use an old laptop running Windows 7 SP1. Nothing fancy. It’s so slow that it refuses to be upgraded or updated.
Last note : I wrote the extra details in case someone uncomfortable with fixing computer stuff stumbles upon this. There might be a simpler way or a simpler fix. I don’t know. I just know this did the trick in my case and hope I can help someone.
Thank you thank you thank you!! This is one San Diego gal who was very frustrated with this DST root issue however the issue was solved!! #33 was extremely helpful! My life can resume and a big thank you, Stephen, for placing this information on the web! All the best, Alicia
I tried clicking on the the 2 fiixes you provided for the cert that expired.
I get a screen immediately that says the site has an unsecure connection.
I
How do I circumvent that?
I tried with Google & Opera with the same result-denied access.
Thank you!
Don
Hi Don,
Try hitting “continue anyways” and it should work.
Cheers mate! Excellent work – Will follow
Thank you Stephen (and Paul, comment 21, I’m on a Mac, too). It has been driving me crazy for days, and I had no idea what was causing all these website problems, so I didn’t know where to start. I called Apple, and the very nice man was no help at all. “Your computer is old.” It was happening on my husband’s computer which is newer with a different operating system. He finally noticed the certificate issue, which got me to your website. I will bookmark you for future issues. Thanks!!!!
It gives no options. There’s a full-screen prompt with a type bar in the middle stating”
‘this is an unsecure connection’ . There is nothing to select/click on.
This will show the prompt: https://letsencrypt.org/certs/isrgrootx1.der
Thanks, Don
Thanks a million my dear friend. I was nearly died with this issue. no one is gave the simplest way to overcome this as you. thank alot.
This was SO helpful!! Thanks, and also thanks KP for the detailed mac instructions. This made it so clear. The only other problem I had was that I couldn’t download the certificates because of the certificate issue, so I had to get a friend to download and send them to me!! Such a waste of time.
All working now thought. Thanks again!
Excelente funcionou perfeitamente!!!!
Hello
I spoke too soon the success of a fix on my Mac in Chrome
I am still getting that stupid Not Secure message on site I use to go to all the time
Not what?
Any Ideas?
Frustrated Susan
Thank you very much, this was extremely helpful! Mine is an older workstation that can’t be updated past OS X 10.11.6, and Chrome was affected but not Firefox. So I downloaded the certificates in Firefox, installed them in the keychain, set them to Always Trust, and now Chrome is back to normal. I am very grateful for your instructions and links.
I use macOS Catalina 10.15.7 and tried to follow the instruction in post #33.
Unfortunately it does not fully work for me: I could install ISRG Root X1 as system, system root and login certificates and also ISRG Root X2 as system and login certificate, but not as system root. For all certificates I put the the trust level to always. However I’m unable to install the let’s encrypt R3 certificate. Nothing happens when I add it to the keychain.
I develop a webapp on my local machine and I get the following error message from the Mailtrap.io email testing service:
ErrorException stream_socket_enable_crypto(): SSL operation failed with code 1. OpenSSL Error messages: error:14090086:SSL routines:ssl3_get_server_certificate:certificate verify failed
Mailtrap gives the following instructions:
Regarding SSL error while trying to send emails to Mailtrap
You are not alone. Please update your OpenSSL version
You might hear about the global issue with Letsencrypt certificates: its old root certificate expired on Sep 30. Mostly it impacted clients who use OpenSSL versions prior 1.1.0. The most common solution is to update your OpenSSL. If you can’t do that read the recipe for v.1.0.2 from OpenSSL.
Any advice would be highly appreciated! Thanks!
Thanks for explaining things in an understandable way! It took your route and with some additional help (how to install certificates on Android 5.1.1) I could solve the problem.
Cheers, Frank
It gives no options. There’s a full-screen prompt with a type bar in the middle stating”
‘this is an unsecure connection’ . There is nothing to select/click on.
This will show the prompt: https://letsencrypt.org/certs/isrgrootx1.der
Thanks, Don
I copied & pasted the link…Both Google & Opera. Each time it immediately came up as an unsecured connection. This happens too often with sites.
I’m stuck, it’s day 5 of this misery. Is there a ‘backdoor’ method of getting the links in order to enact them? Thanks!.
Can you show me how that would look/fit as part of the link?
I apologize for not fully understanding how to use what you wrote in your answer.
Thanks for all of this–and for those who broke it down step by step for tech dummies like me. I fixed it! After six days of not being able to access important sites, this was so much appreciated. THANK YOU!
Thanks so much – I am technologically challenged but I followed your instructions and downloaded what you said to and then trusted the new certificates and it now works properly.
Any idea how to fix this dockerised environment ? I was able to fix in linux system. But not able to do it in our k8s cluster?
Hi Stephen
I’ve clicked on the links to download the 2 new Root CAs but am getting the same error message that was caused by this: NET::ERR_CERT_DATE_INVALID
How can I get around this?
Thanks for your help.
Hello, I have been getting blocked access on certain websites and all of my browsers link the issue back to a certificate called DST Root CA X3. After reviewing your steps of what to download and what to delete, I still cannot get this to work. I cannot locate the certificate, and when I click on these:
ISRG Root X1 (Or ISRG Root X1 DER Format)
ISRG Root X2 (Or ISRG Root X2 DER Format)
Intermediate Certificate (PEM format):
Let’s Encrypt R3 (Or Let’s Encrypt R3 DER Format)
They download but do not allow me to open them. It takes me to my keychain (on my MacBook) and says the root keychain cannot be modified.
How to I proceed?
Thank you
This fixed my old Windows XP Chrome 49
Nothing else worked and I could not find anyone else who truly understands how to fix this problem.
Well done Sir.
I can’t access the links in your fix section. They are blocked behind the very error this is supposed to fix.
Thank you!!! I spent hours searching for a solution, and yours is the only one that worked.
thank you to Greg Hammond for the detailed step by step tutorial. solved the issue that has been driving me crazy
Thanks for the walkthrough and links for getting my browser back up and running. I use an Chrome on an iMac with x.11 and I cannot upgrade for a variety of reasons. This helps keep things chuggin along
Hello Stephen, thanks for writing up this post. It has at least brought little hope to our nightmare we are facing while doing PROD release of changes on Heroku for our prod app and we have got stuck up due to this SSL expiration issue while pushing the code changes via pipeline.
Will only placing below 3 files will solve the issue or do we need to try something else too?
isrgrootx1.der
isrg-root-x2.der
lets-encrypt-r3.der
Hi Divya,
You only actually need the two root certificates only actually.
Thanks Stephen for your quick response.
Hello Stephen,
We are using Heroku for source management and due to dst-root-ca-x3-expiration, we are facing many problems in further deployment process.
I have downloaded ISRG_root_x1.pem & ISRG_root_x2.pem and combined them with name ISRG_combined.pem.
Now, to add a certificate to an app on Heroku, following is the command:
heroku certs:add [CERTIFICATE_NAME] [KEY_NAME]
Here, we will use the ISRG_combined.pem certificate but from where we will get the certificate key?
Thank you
Hello, I don’t understand your question. Those are the only certificates you need. There is no additional key.
Thank you for your response.
I was in the wrong direction but got the correct approach now.
Thank you Sir!
Thank you so much for putting this together. Like other users who have commented I was unable to access many websites on my old laptop. This worked like a charm.
Thanks! My older macbook pro and a much older ipad that I use to watch videos while piddling around just stopped being able to load the content.
Your fixes worked flawlessly! In the meantime I bought a bluetooth adapter for my PC laptop that doesn’t have bluetooth (for external speaker) and this was a pain to move to the man cave and back all the time. And running down the battery faster than I wanted. You have helped to simplify life back to the easy stuff and now I can learn how to use my new airbrush!
Thanks mate, you’re a legend.
i use IMAC late 2009 Google Chrome
if i download these certificates above .pem extensions and double click each..
Keychain tells me under Login that ISRG Root X1 and Root X2 are not trusted. what should i do?
In Google Chrome i get many untrusted website warnings all the time / http(s) warnings this site is not trusted etc
Hi Jeroen, mark the root certificates as trusted.
thanks Stephan. indeed what i did I marked them as trusted and i was asked to fill in Admin password for this computer and reload browser. and indeed it worked. so thanks!
Hi Stephen,
Thank you for your article. I download the certificate but I don’t see what’s the next step on Mac.
hanks again,
F.
Hi Stephen,
I figure out what was the next step with a previous/answer — Thank you so much, Stephen!
F.
What a life-safer! I was actually prepared to reinsatll my OS because I thought my machine caught malware or something. Suffered 20 days typing “thisisunsafe” in my Chrome browser for lots of websites before finding this article. Thank you so much!
Ok pour mon vieux PC sous XP.
Merci à toi.
I’m on a older Mac running OS 10.11.6 and I was wondering do I use the ISRG Root X1 (Or ISRG Root X1 DER Format)
ISRG Root X2 (Or ISRG Root X2 DER Format). Which makes the most sense for my computer, the DRE or non DER format… Please advise
HI Sandy,
Both Root CAs are required. As for the format, I’m not sure what Mac’s prefer, but DER might work better.
Is it possible this is causing my Jave update to fail? I’ve installed the new certificates but I continue to get the “Failed to install Java…Use -allowUntrusted to override.” message.
I’m not sure, but if they are using DST root Certificates, then it very well could be!
Hi, Stephen, I’ve Windows7 Ult, isrgrootx1, isrg-root-x2 and lets-encrypt-r3 I imported it into the ‘Trusted Root Certification Authority’ and I still have the same problem displaying some sites.
Hi Problems persist,
Are you sure that the issue you are experiencing is being caused by this specific issue?
If you imported the two Root CA’s in to your Trusted Certification Store on the Computer account (not your user account), everything should be working. I might recommend restarting your computer however this shouldn’t be required.
Cheers,
Stephen
Hi Steven, should I delete the non-DER versions first before adding the DER versions? -Sandy
Hi Sandy,
Those are just files so it doesn’t matter.
I also imported ‘IdenTrustCommercialRootCA’ and after restarting the computer everything looks O.K. Thanks very much.
This solution works! Thank you sir!
I could not download the certificates via Chrome (running on Windows XP). My workaround solution was to open this page via Firefox (again running on XP) and save the three *.der files provided by Stephen to a temporary folder – by right clicking each link he provided and selecting “Save Link As …”. I did not try to download the *.pem files, just the *.der files.
The next step was to press and hold the Windows icon key and then press the “r” key on the keyboard. This opens the Run command box. Then type “certmgr.msc” in the Open command line and click OK. The “Certificates” browser will open up.
The next step is to locate and delete 3 items:
R3 Certificate and DST ROOT CA X3 (one of these two certificates appears in two of the folders)
Look for the three instances in 3 sub-folders:
1. Trusted Root Certification Authorities > Certificates
2. Intermediate Certification Authorities > Certificates
3. Third-party Root Certification Authorities > Certificates
Make a note of which certificate is in which folder (needed later). Right click each instance of the certificates, and delete.
Once the three files are deleted, select the “Action” menu item in the header of the Certificates browser, then select All Tasks > Import. This will open a Certificate Import Wizard. Click Next and browse to the temporary location where the *.der files were stored. Change the “Files of type” to All Types (*.*), select one of the *der files, and click “Open”. Select the appropriate folder (as noted above) and place the *.der file accordingly. Repeat for the remaining 2 files.
This worked immediately for me (did not have to reboot).
Thank you so much!!!!!! I’ve been through a month with problem on chrome and steam and now it’s working again. Do you how can I fix globalsign atlas r3 dv tls ca 2020 error? For those who can’t fix, you should install in the option ”Place all certficates in the following store” on ”Trusted Root Certification Authorities”
I run Windows 7 SP1, I typed “certmgr.msc” and followed the instructions, where I deleted and ‘replaced’ the certificates in the folders. Still the same problem, nothing helped :/
I can’t download the certificates because the download links lead me to an “invalid certificate” page. Does anyone know if there is another way to download the certificates?
I’m running Mac OS 10.11.6. I could not install the .pem files into Keychains > System Roots folder (in upper left panel). However, I did install them in the Keychains > System folder just fine (admin password box was buggy and took a few attempts). Then I right-clicked on each file, selected Get Info, clicked on the Trust arrow to expand and selected “Always Trust” for “When using this certificate.” Then closed.
I went to a couple problem websites and they loaded fine! PS — I did not have to restart.
Thanks much!
i loaded new certs but pages load very slowly and I even get the same error page” cert invalid or something” and after 3-4 seconds it than resolves the URL on its own and loads the https web site any idea – almost seems like the new certs did help but a conflict remains that keeps bring up the cert error message before the web sites resolve.
Thank you so much!!
Thank you for this! Been wondering what the hell was going on for the last month lol. Issue fixed on Chrome on MacOS El Capitan. Just needed to hit Get Info on the certificates once in Keychain Access and set trust to Always Trust and restart my browser.
Thanks again!
I was facing problem since Oct connecting Defi Websites, thanks to your article, it resolved my issue.Mu
Thanks for the information provided here. This was such a simple solution and didn’t require me to update OS or turn off security for it to work. Appreciate what you do!
Thanks, Stephen! And thanks for the step-by-step instructions for Mac, Kp! Fabulous!
Hello:
I followed the instructions and it works on my browser. The problem I’m having is that (removed external link) site have http services which I need to consume. When I check the page certificates everything appears normal with the new chain. When I go to use HTTP post command or visit the site eventhough the page certificates chain appears ok always the deleted old DST certificate returns to my certificate store, maybe is something of the site for compatibility, but since I deleted my old R3 issued by DST my post command don’t work anymore. Do you know a site I can download this R3 older file? Would rather have the certificate error message and the service working than no error message and no response from the server.
Hi Aida,
The DST web link in this post should have the older certs still listed unless they have removed them from the page.
Cheers
Stephen
Thanks for the response, the problem is that they are not listed on the certificates in the page but when I go to the page or use the post command the deleted DST reappears and I don’t find anywhere to download the old R3 since only the DST reappeasrs, the site says certificate ok on the browser and when I look at the chain is the new chain, no signs of DST or old R3 anywhere.
Thank you Sir, Great tips, its works!
I am not sure if I have to delete the certificates first as some say or not? Akso do I need all 3 or just the first 2.I am on windows 7 and when I install them, it tells me not to trust them, so I am afraid to install, did others have this issue?
Also I am curious why I dont have this issue as well as sites with Java script not working in Chrome but are ok in Firefox, even though java is enabled? Is this part of the problem?
Hi Stephen,
Thanks so much for this post (and thanks to everyone who has commented). This issue was driving me nuts, but you have found the solution. Well done!
One issue I’m having (and maybe others are too) is that about a week or so after I delete the DST Root certificates and install the new ones, the old ones come back, and the problem starts all over again. If I do the remove/install procedure everything is fine, but how can I prevent the deleted certificates from returning?
Thanks in advance for your help,
Theran
[email protected]
P.S. I’m running Windows 10 on an HP core i3 laptop, and am using a PiHole DNS sinkhole on my LAN.
If you are on Windows 7 just follow detailed step-by-step instructions by Bob, comment #64. Thanks Bob, you helped me a lot!
Stephen, looks like I’m late to the discussion, but here goes.
OSX 10.11.6
Downloaded (3) pem’s . . .
isrgrootx1.pem
isrg-root-x2.pem
lets-encrypt-r3.pem
— “Installed” the files via the keychain app
— I now see them in System | All Items
— Restarted
— Issue not resolved: in Chrome, SSL privacy errors
— -and- a red “x” displays next to the file in Keychain, indicating “not trusted”
Please advise. Thank you!
RESOLVED **
In Keychain changed Getinfo to “always trust”
Stephan et al — you saved me from therapy. Thank you.
I want to download a DST Root CA Xe
I need help, and I’ll be honest man, None of this is my wheelhouse. Could you PM me and walk me through all this?
Good job Stephen. Dziękuję. 😉