Today I wanted to do a brief post addressing Microsoft Exchange Backup and Disaster Recovery.
In the past week I’ve had over 30 people reach out to me via chat looking for help and advice in situations where:
- A Cumulative Update Failed
- Exchange Services will not start
- Hardware Failure Occurred
In all of these cases the admins took a snapshot of their Exchange virtual machine (in Hyper-V or ESXi/VMware), and then restored it to the previous point when the failure occurred. This completely broke their Exchange install and possibly made it unrecoverable.
The above example is what you DO NOT want to do.
Microsoft Exchange Aware Backups
As per: https://docs.microsoft.com/en-us/exchange/high-availability/disaster-recovery/disaster-recovery?view=exchserver-2019
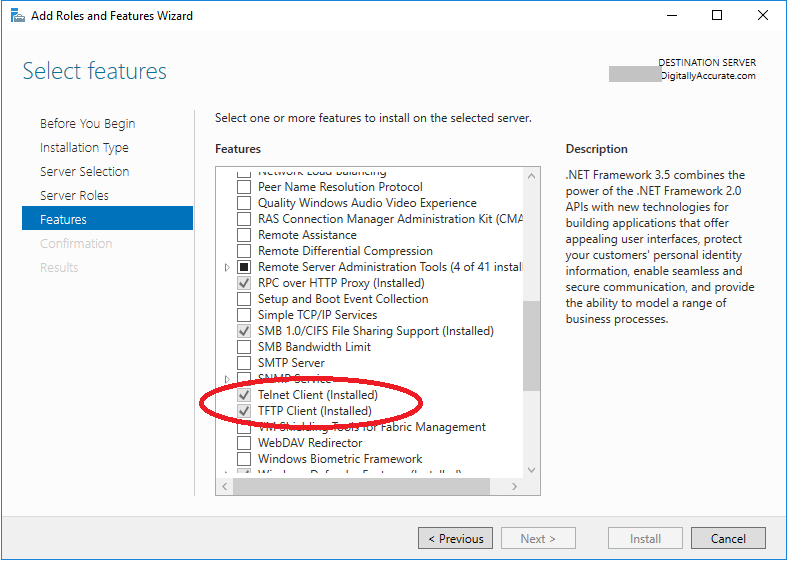
Exchange Server supports only Exchange-aware, VSS-based backups. Exchange Server includes a plug-in for Windows Server Backup that enables you to make and restore VSS-based backups of Exchange data. To back up and restore Exchange Server, you must use an Exchange-aware application that supports the VSS writer for Exchange Server, such as Windows Server Backup (with the VSS plug-in), Microsoft System Center 2012 – Data Protection Manager, or a third-party Exchange-aware VSS-based application.
You must use an Exchange-aware backup and/or disaster recovery application/software suite. These applications are aware of Exchange and designed to perform proper backups of Exchange, the mailboxes, and configuration. Not only do they backup the mailbox database and the VM running Exchange, but they also backup the system state and configuration of Microsoft Exchange.
Simply performing a VM snapshot is not supported and can break your Exchange installation.
Note that the configuration for Microsoft Exchange is stored inside of Active Directory, and not on the actual Exchange Server. Restoring the Exchange Server to a previous snapshot will cause a configuration synchronization gap between the Active Directory configuration and the mailbox database on the Exchange Server.
Options for Backup
There are plenty of options to perform Microsoft Exchange-aware backups.
If you’re looking for something free and easy, you could use the built-in Windows Server Backup function on Microsoft Windows Server. It’s perfect for special migration and upgrade jobs, homelabs, and small/micro sized businesses.
For larger organizations, I’ve used, setup, implemented, and managed the following backup applications:
There’s no excuse for not having a backup, especially if you call yourself a professional. You should always have a full working backup, especially before performing any type of maintenance, updates, or upgrades to your environment.
Microsoft Exchange Issues and Failures
Additionally, in the event of an issue, the solution isn’t always to restore from backup.
In most cases when something fails, it’s best practice to troubleshoot and correct the issue, instead of blasting away Exchange and restoring from backups.
Most Exchange installs can be saved simply by following standard troubleshooting procedures. Even if an Exchange Cumulative Update fails, you can fix what caused it to fail, and then re-run the installer/upgrader to attempt to recover! No backup restore needed!