In a VMware Horizon environment with DUO MFA configured via RADIUS on the VMware Horizon Connection Server, you may notice authentication issues when logging in through a UAG (Unified Access Gateway) after upgrading to VMware Horizon 8 Version 2111.
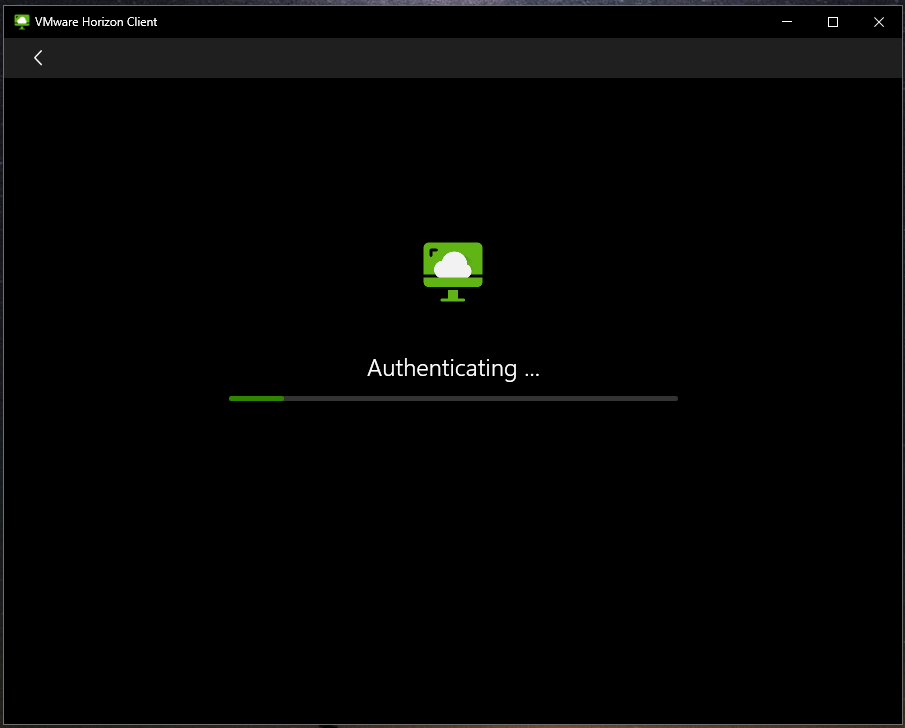
During this condition, you can still login and use the connection server directly with MFA working, however all UAG connections will get stuck on authenticating.
Disabling MFA and/or RADIUS on the connection server will allow the UAG to function, however MFA will be disabled. This occurs on upgrades to version 2111 of the UAG both when configuring fresh, and importing the JSON configuration backup.
Temporary Fix
Update January 26 2022: VMware has now released version 2111.2 of the Unified Access Gateway which resolves this issue. You can download it here, or view the release notes here.
Update January 12 2022: It appears VMware now has a KB on this issue at: https://kb.vmware.com/s/article/87253.
Temporary workaround/fix: To fix this issue, log on to the UAG and under “Horizon Edge Settings”, configure “Client Encryption Mode” to “Disabled”.
“Client Encryption Mode” is a new setting on UAG 2111 (and UAG 2111.1) that enables new functionality. Disabling this reverts the UAG to the previous behavior of older Unified Access Gateway versions.
More information on “Client Encryption Mode” can be found at https://docs.vmware.com/en/Unified-Access-Gateway/2111/uag-deploy-config/GUID-1B8665A2-485E-4471-954E-56DB9BA540E9.html.
Another workaround is to deploy an older version of the UAG, version 2106. After downgrading, the UAG functions with DUO and RADIUS even though the Connection Server is at version 2111.
If you use an older version of the UAG, please make sure that you mitigate against the Apache log4j vulnerabilities on the UAG using information from the following post: https://kb.vmware.com/s/article/87092.
Have same issue, but found out dropping clients to 8.3 also resolves it. What version conn server are you running when you had the issue?
Hi Ricky,
This occurred when I updated my entire infrastructure (Clients, Connection Server, and UAG) from 2106 to 2111.
It’s nice to know someone else is having the issue.
Cheers,
Stephen
Hi Stephen,
Do you know if this also affects Azure MFA when configured with the NPS extension?
We are currently running on Horizon 2106 including the matching UAG and were looking at moving to 2111 until I heard about this from others.
Hopefully VMware are aware of the issue and will issue a fix soon.
Greig
I have upgraded our test/dev environment to 2111 and configured it with Azure MFA through the NPS extension. All works as expected.
This issue occured when MFA configured on Connection Server, but worked well when MFA configured on UAG.
That is correct, this issue only occurs if MFA is configured on the connection server.
This issue does not happen when MFA is configured on the UAG itself.
just implementing MFA and didnt understand why it didnt work on UAG.
Thanks this saved me a hole lot of time
Glad it helped Bjorn!
Hi
here same issue but with error on the client ‘The required security cryptography for this service failed. Please contact your Administrator.’
After set “Client Encryption Mode” to disable in UAGs, works like a charm.