
If you are running Microsoft Windows in a domain environment with WSUS configured, you may notice that you’re not able to install some FODs (Features on Demand), or use the “Turn Windows features on or off”. This will stop you from installing things like the RSAT tools, .NET Framework, Language Speech packs, etc…
You may see “failure to download files”, “cannot download”, or errors like “0x800F0954” when running DISM to install packages.
To resolve this, you need to modify your domain’s group policy settings to allow your workstations to query Windows Update servers for additional content. The workstations will still use your WSUS server for approvals, downloads, and updates, however in the event content is not found, it will query Windows Update.
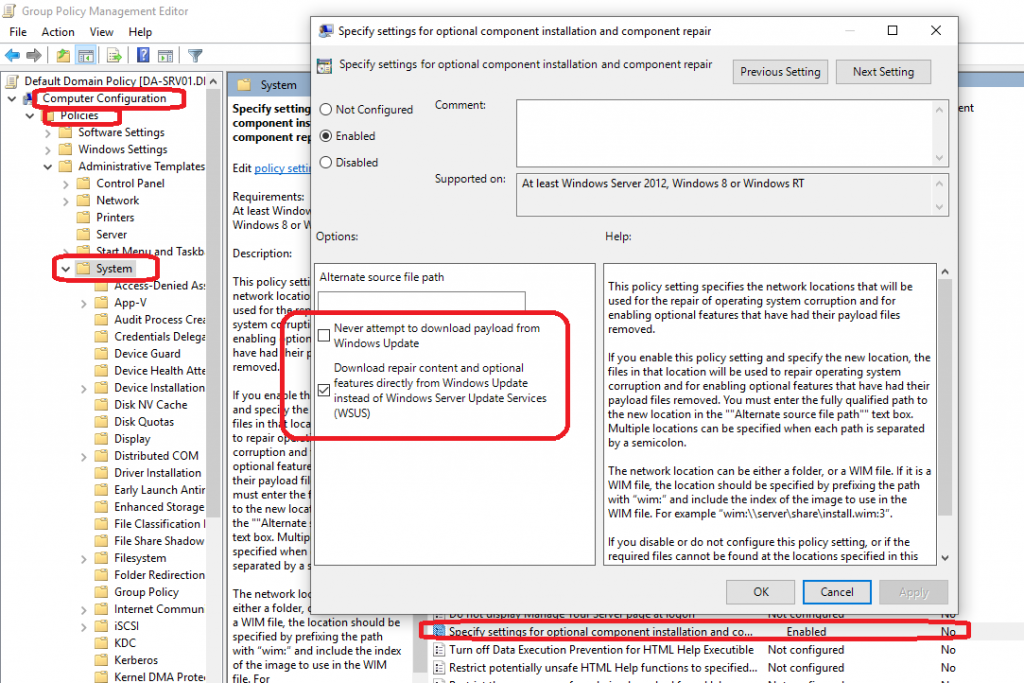
Enable download of “Optional features” directly from Windows Update
- Open the group policy editor on your domain
- Create a new GPO, or modify an existing one. Make sure it applies to the computers you’d like
- Navigate to “Computer Configuration”, “Policies”, “Administrative Templates”, and then “System”.
- Double click or open “Specify settings for optional component installation and component repair”
- Make sure “Never attempt to download payload from Windows Update” is NOT checked
- Make sure “Download repair content and optional features directly from Windows Update instead of Windows Server Update Services (WSUS)” IS checked.
- Wait for your GPO to update, or run “gpupdate /force” on the workstations.
Please see an example of the configuration below:
Download repair content and optional features directly from Windows Update instead of Windows Server Update Services (WSUS)
You should now be able to download/install RSAT, .NET, Speech language packs, and more!
[…] *Please Note: If you are using WSUS, you may not be configured to download “optional features” from Windows Update (resulting in “cannot download”, or “0x800F0954”). To resolve this, please follow the instructions at: https://www.stephenwagner.com/2018/10/08/enable-windows-update-features-on-demand-and-turn-windows-f… […]
Hi Stephen. I’m trying it on my Windows 2008 R2 and there is no “Specify settings for optional component installation and component repair” option…
Hi Cristian,
Is your server fully up to date? I’m wondering if 2008 R2 doesn’t support support these GPO options in that version of Active Directory.
2008 R2 is reaching end of life soon. When you upgrade I think it should become available.
Cheers,
Stephen
Hi Stephen,
Just wanted to say thanks for this post.
Added it to my deployment plan for networks and it totally fixed my problem.
To Christian: If you look at the window above in the screenshot, you can see that this setting is only supported on Windows 2012, Windows 8 or Windows RT. It is not applicable to Server 2008R2
I just wanted to join in thanking you so very much for posting this information. You saved me a tonne of time.
Second time you saved me…
Glad I could help Pawel!
Cheers,
Stephen
I’ve found that even with that oolicy enabled, we still could not install RSAT as a FOD. This is because we also have “Computer Configuration -> Administrative Settings -> System -> Internet Communication Management -> Internet Communication settings -> Turn off access to all Windows Update features” enabled. The reason we normally have that policy enabled is because it prevents Device Manager from automatically installing driver updates. We want to control the drivers installed in our environment.
PS C:\WINDOWS\system32> DISM.exe /Online /add-capability /CapabilityName:Rsat.ActiveDirectory.DS-LDS.Tools~~~~0.0.1.0
Deployment Image Servicing and Management tool
Version: 10.0.17763.1
Image Version: 10.0.17763.316
[==========================100.0%==========================]
Error: 2
The system cannot find the file specified.
The DISM log file can be found at C:\WINDOWS\Logs\DISM\dism.log
Thank you, thank you, thank you.
I have been trying to solve this for weeks and finally did the right google search to find this post.
Thank you for this post i finally go them to install will also properly work via the GUI as well now
You’re awesome!
Hmmm. I’ve enabled the “Specify settings for optional component installation and component repair,” turned on “Download repair content and optional features directly from Windows Update instead of Windows Server Update Services (WSUS),” but I still get this error:
Deployment Image Servicing and Management tool
Version: 10.0.17763.1
Image Version: 10.0.17763.529
[==========================100.0%==========================]
Error: 0x8024002e
DISM failed. No operation was performed.
For more information, review the log file.
The DISM log file can be found at C:\WINDOWS\Logs\DISM\dism.log
I’d recommend checking the log file to see what’s going on.
Also, maybe try a “gpupdate /force” and restart. Then try again as well.
“0x8024002e” is usually a windows update error, so I’m wondering if the GPO hasn’t been applied (gpupdate should fix this), or if your Windows Update components may be corrupted. You might have to reset your Windows Update. If you’re managing your Windows Updates with a 3rd party application, this may also cause this issue.
Stephen
On item #4, using Windows 8.1 Home edition, “Specify settings for optional component installation and component repair” is not on the list. How can I update the list?
Hi Steve,
If it’s not there, I’m wondering if you’re administrative templates for your GPO are old and out of date.
I think you can either download the GPO Administrative Templates, or grab them off a Windows 10 computers (or newer Windows Server), and add them to your AD Template Store, then the option should become available.
Cheers,
Stephen
I’ve been having this problem for YEARS, and eventually just took it as a fact of life that I will need to specify source files from Windows Media in some WSUS environments. Thank you SO MUCH for this post.
There is truly no reason this policy should not be in the “Windows update” container in GPedit, or the repair/content files should be automagically imported to WSUS when you enable feature on demand.
What if your environment, including all domain controllers, WSUS, and workstations, are in a closed room with no possible internet access/connection? If the WSUS repository here has been manually seeded offline and works for other updates, will this solution work as long as “Feature Packs” is selected for an update classification? Are there any other update classifications required to be selected in addition to Feature Packs? We already have the other necessary ones selected and synchronized offline and working in the closed environment. I read somewhere else that “Updates” needed to be selected as well, but we are trying to avoid selecting unnecessary classifications in order to keep the amount of data down because it’s a bit of a chore to get it into the closed room. It’s for a military contract in case you are wondering.
Hey Vinnie,
That’s a tough one. The resolutions I’ve posted allow the Windows workstations to bypass WSUS to install Features or Roles. Having them completely cut off kinda breaks that, lol.
If you’re doing this for Features and Roles, I don’t think this will work for your scenario. To load them offline, I don’t even know if this is possible (I haven’t Google’d it), but could you put a Windows ISO on a network share, and use DISM to install components or roles you need for your specific use case?
As for Updates:
Your case is interesting, because typically in most environments there’s the master synchronization, and then as clients contact WSUS, admins approve updates that are “Needed”. After an admin approves the “needed” update, WSUS will reach out and download the update making it available to the host.
For offline synchronization, in a use case where you can’t have that back and forth communication to sync/download only “needed” and approve from there, technically you’d need to synchronization all categories, and then approve all updates which would probably be 100’s of GB or even possibly TBs of data. In this case I’d highly recommend using WSUS with SQL, instead of the WID (Windows internal Database), and make sure your keep the WSUS database clean. In that case, you’d have all the updates but the problem is that they would all be approved and installed.
I don’t even know if this is possible, but you might need to have two WSUS servers, one where everything is approved, so it offline downloads all updates, and then downstream have a secondary one that the computers report to so you can manually approve when you want.
I hope this helps, sorry I don’t have more exact info.
Stephen
This does not work on 1909
Hi Jimmy,
It does work on 1909. I’d recommend checking your Syntax and trying again.
Cheers,
Stephen
Hi Stephen,
I and others on 1909 have found that the GPO “Specify settings for optional component installation and component repair” is no longer located in “System”. Instead, it is located in “All Settings”.
I have verified this on Windows 10 Education, and will verify on Pro in a few hours.
Regards,
GS.
Hi Stephen. I’ve been missing RSAT for ages and attempting many fixes to get it though optional features (which are empty on our WSUS setup) and tried many different options. This has finally given me a solution that works. Thanks so much.
Cheers
Stephen,
Thanks so much for this work around. It has been used many times for members of my team needing the Japanese Language Pack and keyboard.
Many thanks!
Greg
Thank you!
Do you know what ADMX file updates the system policy? I have Server 2012R2 and dont notice that option to specify. Thanks in advance.
Hi Mike,
Sorry but I don’t actually know off the top of my head. You might need to look at Microsoft’s documents, or just try updating all the ADMX files.
Cheers,
Stephen
Hi Steve,
Should “Specify settings for optional component installation and component repair” = Enabled, allow the “Add a language” feature in Settings app show all available Language FODs (i.e. Display language, Text-to-speech, Speech recognition, Handwriting) from Windows Update? Also, is the above GPO setting impacted if you have “Do not connect to any Windows Update Internet locations” = Enabled?
Thanks,
Tim
Hey Tim,
If the system is trying to pull an FoD like a language pack or language speech pack, applying this fix will allow it to bypass the WSUS and install it.
As for your second question, I’m not quite sure. You’d have to test it.
Cheers,
Stephen
Hi Steve,
Appreciate your response. I just tested using Add a Language with the following GPO settings – “Specify settings for optional component installation and component repair” = Enabled as you advised. Also “Do not connect to any Windows Update Internet locations” = Not Configured, and “Remove access to use all Windows Update features” = Not Configured. It still does not work when signed on as a non-administrator. It does partially work when signed on as an administrator, in that it will download the language features, but not the language pack. Perhaps it is working as designed.
Thanks,
Tim
Hi Timothy,
I might recommend rechecking all your config and verifying that you don’t have any other GPOs interfering with the settings.
Technically everything should be working. I’ve deployed this to numerous environments I manage with hundreds of users and computers at my clients and it works smooth with no issues. I’ve also assisted customer deploy this to their own environments with 100s and 1000s of computers.
I can’t remember if I said this, but after modifying the GPOs, give them time to replicate and run a “gpupdate /force” on a workstation to test.
Also, make sure you’re not doing any HTTPS/SSL scanning or interception with Microsoft servers as this could also stop things from working.
Stephen
You save my day!
Hello, thanks for sharing this post.
I’m getting the error 0x8024002e while trying to apply FOD, but all other Windows Updates from our WSUS server works fine.
This is an extract from the dism.log file:
2020-06-01 16:44:34, Error DISM DISM Package Manager: PID=11512 TID=13656 Failed finalizing changes. - CDISMPackageManager::Internal_Finalize(hr:0x8024002e)
2020-06-01 16:44:34, Error DISM DISM Package Manager: PID=11512 TID=13656 Failed processing package changes with session options - CDISMPackageManager::ProcessChangesWithOptions(hr:0x8024002e)
2020-06-01 16:44:34, Error DISM DISM Package Manager: PID=11512 TID=13656 Failed to install capability. - CPackageManagerCLIHandler::ProcessCmdLine_AddCapability(hr:0x8024002e)
2020-06-01 16:44:34, Error DISM DISM Package Manager: PID=11512 TID=13656 Failed while processing command add-capability. - CPackageManagerCLIHandler::ExecuteCmdLine(hr:0x8024002e)
2020-06-01 16:44:34, Info DISM DISM Package Manager: PID=11512 TID=13656 Further logs for online package and feature related operations can be found at %WINDIR%\logs\CBS\cbs.log - CPackageManagerCLIHandler::ExecuteCmdLine
2020-06-01 16:44:34, Error DISM DISM.EXE: DISM Package Manager processed the command line but failed. HRESULT=8024002E
Any idea?
Thanks
HI Frank,
You’ll need to look at the logs (CBS.log) and see what it’s saying.
Stephen
There are issues if you have this enabled:
Computer Configuration\Administrative Templates\System\Internet Communication Management\Internet Communication Settings\Turn off access to all Windows Update feature. Registry Value: DisableWindowsUpdateAccess
If you disable this GPO, the FOD works.
But in our case we don’t want that users can download updates directly from Microsoft.
Any other idea?
Thanks
Technically the only thing that should become available is the FoDs. The users shouldn’t have access to do anything else.
Thank you for posting this guide. Like others have said, this is the only place I found instructions to fix this issue for domain-joined computers. All the other sources I checked had solutions for Workgroup computers.
Hey Apollo, I’m glad to hear!
I’ve the same issue as Frank.
We don’t want that users can download updates directly from Microsoft – but I can’t find a way.
Any Ideas?
Hi Daniel,
If you have WSUS and have your GPOs configured properly, your users won’t be able to download updates.
Cheers,
Stephen
A quick update on my issues with installing Language FODs as Standard User. The reason it only worked as Administrator was due to no GPOs applying, so it was an issue with GPO restrictions as you suggested. Interestingly, what I discovered is that if you have “Turn off Store application” set to Enabled then it will prevent installing any Language FODs as uses the Store as the source. Even without any GPO restrictions to the Store, I am still not able to install Language FODs as a Standard User, only as an Administrator. However you can install Language Packs as a Standard User.
Hi i have windows 2019 standard WSUS server newly built , but i am not able to see my domain controllers which is core 2019 server listed in the domain controllers in the WSUS console.Is there any know compatibility issues? I have checked everything but fail to find a fix.
Hi Adam,
Most likely the GPO specifying the WSUS server isn’t applying to the domain controllers. Also, after confirming the GPO you will need to check for updates using “sconfig”.
Cheers,
Stephen
really appreciate it! saves me from restless research and fixed the installing language pack issue.
hi guys
is the same gpo edit for version 2004?please help as its urgent.i tried to download the chinese package however the packages are not saving at software distribution folder
This helped with getting .Net Framework installed on Server 2019. Thanks stranger!
Hello,
Using domain joined Win10 machines (20H2) and ending up with an error code in PS of 0x80d05001 when trying to install RSAT.
I know this is an enabled GPO causing this issue (moved it to OU with no GPOs and success). Just trying to find out exactly which one would actually cause this error.
I have checked the following GPOs:
Computer Configuration -> Administrative Settings -> System -> Specify settings for optional component installation and component repair. This is enabled and checked to DL from WinUpdate.
Computer Configuration -> Administrative Templates -> System -> Internet Communication Management -> Internet Communication settings -> Turn off access to all Windows Update features. This is NOT CONFIG
Computer Configuration -> Administrative Templates -> Windows Components -> Windows Update -> Do not connect to any Windows Update Internet locations. This is NOT CONFIG
So far I haven’t been able to tell which enabled GPO I must be missing that is not allowing the machines to download any RSAT modules. Digging further, but any hints are much appreciated if there are others that could lead to this error.
[…] Enable Windows Update “Features on Demand” and “Turn Windows features on or off” in WSUS Env… […]
You are a titan Thanks.
You manage a network with four domain controllers running Windows Server 2016, seven member servers running Windows Server 2016, four member servers running Windows Server 2012 R2, 100 Windows 10 computers, and 35 Windows 8.1 computers. You need to maintain updates and patches on all these computers. Explain how you would set up WSUS to do so. Which WSUS features would you use? What method would you use to allow you to target specific computers with different types of updates? What method would you use to configure Windows Update on client computers?
Hi Ernest,
You’d simply implement WSUS, configure GPOs, create your AD OU structure, and modify all the configuration to reflect what you’re trying to achieve.
Cheers,
Stephen
[…] Enable Windows Update “Features on Demand” and “Turn Windows features on or off” via GPO as provided here: https://www.stephenwagner.com/2018/10/08/enable-windows-update-features-on-demand-and-turn-windows-f… […]
Wanted to say ‘Thanks’ for this quick article. Like many struggling with WSUS, and recent MS “Un-Deployments”, our small team just hasn’t had the time or the environment to properly test various iterations of these GPOs
Will test your recommendations. If successful, will save a Butt-load (Technical Term?) of time and effort
JR
Happy if the post helped JRushing! 🙂
been using this post now going on 4/5 years for this issue, I always remember this article when i hit it this issues, so thanks